This Services Guide contains provisions that define, clarify, and govern the services described in the quote that has been provided to you (the “Quote”) and which are subject to the Master Services Agreement between Wheelhouse IT and you (located at https://www.wheelhouseit.com/master-service-agreement/ (“MSA”)) . If you do not agree with the terms of this Services Guide, you should not sign the Quote and you must contact us for more information.
This Services Guide is our “owner’s manual” that generally describes all managed services provided or facilitated by Wheelhouse IT (“Wheelhouse,” “we,” “us,” or “our”); however, only those services specifically described in the Quote will be facilitated and/or provided to you (collectively, the “Services”). Capitalized terms that are not defined in this Services Guide are defined in the MSA.
Activities or items that are not specifically described in the Quote will be out of scope and will not be included unless otherwise agreed to by us in writing in an amendment to the Quote or, if applicable, in a new Quote.
This Services Guide contains important provisions pertaining to the auto-renewal of the Services in the Quote, as well as fee increases that may occur from time-to-time. Please read this Services Guide carefully and keep a copy for your records.
If an Initial Audit / Diagnostic Services are listed in the Quote, then we will audit your managed information technology environment (the “Environment”) to determine the readiness for, and compatibility with, ongoing managed services. Our auditing services may be comprised of one or more of the following:
If deficiencies are discovered during any initial audit / diagnostic service or onboarding service, we will bring those issues to your attention and discuss the impact of the deficiencies on our provision of the Services and provide you with options to correct the deficiencies. Please note, unless otherwise expressly agreed by us in writing, initial audit / diagnostic service and/or onboarding services, do not include the remediation of any issues, errors, or deficiencies (“Issues”), and we cannot guarantee that all Issues will be detected. Issues that are discovered in the Environment may be addressed in one or more subsequent quotes.
If onboarding services are listed in the Quote, then one or more of the following services may be provided to you.
This list is subject to change if we determine, at our discretion, that different or additional onboarding activities are required.
If deficiencies are discovered during the onboarding process, we will bring those issues to your attention and discuss the impact of the deficiencies on our provision of our monthly managed services. Please note, unless otherwise expressly stated in the Quote, onboarding-related services do not include the remediation of any issues, errors, or deficiencies (“Issues”), and we cannot guarantee that all Issues will be detected during the onboarding process.
The duration of the onboarding process depends on many factors, many of which may be outside of our control—such as product availability/shortages, required third party vendor input, etc. As such, we can estimate, but cannot guarantee, the timing and duration of the onboarding process. We will keep you updated as the onboarding process progresses
Ongoing/recurring services are services that are provided to you on an ongoing basis and, unless otherwise indicated in a Quote, are billed to you monthly. Some ongoing/recurring services will begin with the commencement of onboarding services; others will begin when the onboarding process is completed. Please direct any questions about start or “go live” dates to your technician.
Implementation and facilitation of a backup and file recovery solution from our designated Third Party Provider. · 24/7 monitoring of backup system, including offsite backup, offsite replication, and an onsite backup appliance (“Backup Appliance”) · Troubleshooting and remediation of failed backup disks · Preventive maintenance and management of imaging software · Firmware and software updates of backup appliance · Problem analysis by the network operations team · Monitoring of backup successes and failures · Daily recovery verification Backup Data Security: All off-site backed up data is encrypted in transit and at rest in 256-bit AES encryption. All facilities housing cloud backed ups of data implement physical security controls . Backup Retention: Unless otherwise indicated in the Quote, backed up data will be retained on a rolling basis in accordance with the following retention periods:
Backup Alerts: Backup software will be configured to inform of any backup failures. Recovery of Data: If you need to recover any of your backed up data, then the following procedures will apply: · Service Hours: Backed up data can be requested during our normal business hours. · Request Method. Requests to restore backed up data should be made through one of the following methods: o Email: [email protected] o Web: https://www.Wheelhouse IT.com/support o Telephone: Posted on the customer web portal · Restoration Time: We will endeavor to restore backed up data as quickly as possible following our receipt of a request to do so; however, in all cases data restoration services are subject to (i) technician availability, (ii) confirmation that the restoration point(s) is/are available to receive the backed up data, and (iii) availability and limitations of internet connectivity. |
Implementation and facilitation of a backup monitoring solution from our designated Third Party Provider. Features include:
If you purchase one or more blocks of technical support or consulting hours from Wheelhouse IT, then we will provide our professional information technology consulting services to you from time to time on an ongoing, “on demand” basis (“BoH”). The specific scope, timing, term, and pricing of Services to be rendered during the BoH (collectively, “Specifications”) will be determined between you and us at the time that you request such Services from us. You and we may finalize the Specifications (i) by exchanging emails confirming the relevant terms, or (ii) by you agreeing to an invoice, purchase order, or similar document we send to you that describes the Specifications (an “Invoice”), or in some cases, (iii) by us performing the Services or delivering the applicable deliverables in conformity with the Specifications. If we provide you with an email or an Invoice that contains details or terms for the Services that are different than the terms of the Quote, then the terms of the email or Invoice (as applicable) will control for those Services only. A Service will be deemed completed upon our final delivery of the applicable portions of Specifications unless a different completion milestone is expressly agreed upon in the Specifications (“Service Completion”). (For example, sales of hardware will be deemed completed when the hardware is delivered to you; licensing will be completed when the licenses are provided to you, etc.) Any defects or deviations from the Specifications must be pointed out to us, in writing, within ten (10) days after the date of Service Completion. After that time, any issues or remedial activities related to the Services will be billed to you at our then-current hourly rates. Unless we agree otherwise in writing, Services under a BoH will be provided only during our normal business hours. Services provided outside of our normal business hours are subject to increased fees and technician availability and require your and our mutual consent to implement. The priority given to implementing the Services under a BoH will be determined in our reasonable discretion, considering any milestones or deadlines expressly agreed upon in an invoice or email from Wheelhouse IT. If no specific milestone or deadline is agreed upon, then the Services will be performed in accordance with your needs, the specific requirements of the job(s), and technician availability. BoH time is not refundable, and unused hours comprising the BoH cannot be credited back to you. |
Please see Anti-Virus; Anti-Malware and Breach / Cyber Security Incident Recovery sections below for important details.
All hosted email is subject to the terms of our Hosted Email Policy and our Acceptable Use Policy.
We use different end point solutions for different circumstances and levels of service, which may include:
* Please see Anti-Virus; Anti-Malware and Breach / Cyber Security Incident Recovery sections below for important details.
* Requires at least two layers (e.g., endpoint, email, network, servers, and/or cloud workload.)
Please see Anti-Virus; Anti–Malware and Breach / Cyber Security Incident Recovery sections below for important details.
We assist in setting up training, but Customer, through a “training contact” designated by Customer, runs training:
Please see Anti-Virus; Anti-Malware and Breach / Cyber Security Incident Recovery sections below for important details.
This warranty does not include the time required to rebuild your system, such as the time required to configure a replacement device, rebuild a RAID array, reload the operating system, reload and configure applications, and/or restore from backup (if necessary).
When we refer to such labor charges in an Order, it includes all labor charges for setup of new workstations, or replacement of existing workstations in our offices, and, unless otherwise stated in the Order, remote installation of the workstations with your on-site assistance.
The following restrictions apply:
* Remediation services provided on a time and materials basis. Please see Anti-Virus; Anti-Malware and Breach / Cyber Security Incident Recovery sections below for important details.
The assessment will cover the following five core areas of the NIST framework:
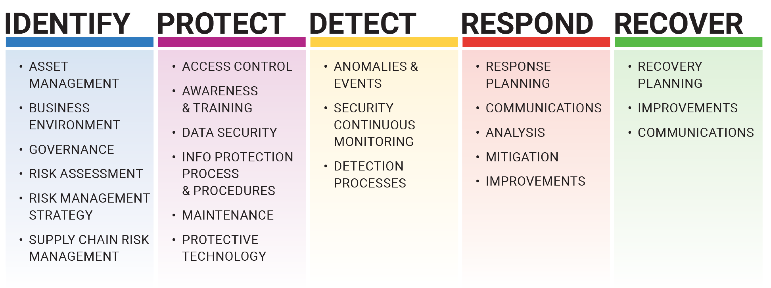
The results of the assessment will be provided in a report that will identify detected risks and your organization’s current maturity levels (i.e., indicators that represent the level of capabilities within your organization’s security program) and will propose actionable activities to help increase relevant maturity levels and augment your organization’s security posture.
Please Note: This service is limited to an assessment/audit only. Remediation of issues discovered during the assessment, as well as additional solutions required to bring your managed environment into compliance, are not part of this service. After the audit is complete, we will discuss the results with you to determine what steps, if any, are needed to bring your organization into full compliance.
External Pen Testing: exposes vulnerabilities in your internet-facing systems, networks, firewalls, devices, and/or web applications that could lead to unauthorized access.
Internal Pen Testing: Validates the effort required for an attacker to overcome and exploit your internal security infrastructure after access is gained.
PCI Pen Testing: Using the goals set by the PCI Security Standards Council, this test involves both external and internal pen testing methodologies.
Web App Pen Testing: Application security testing using attempted infiltration through a website or web application utilizing PTES and the OWASP standard testing checklist.
Please see additional terms for Penetration Testing below.
Software agents installed in Covered Equipment (defined below) report status and IT-related events on a 24×7 basis; alerts are generated and responded to by Wheelhouse IT.
In addition to the above, our remote monitoring and management service will be provided as follows:
YES=depending on availability and practicality.
Event | Server | Workstation |
Hardware Failures | No | No |
Device Offline | Yes | No |
Failed/Missing Backup | Yes | No |
Failed/Missing Updates | Yes | Yes |
Low Disk Space | Yes | No |
Agent missing/misconfigured | Yes | Yes |
Excessive Uptime | Yes | No |
Automatic Reboots | Case by case determination | Case by case determination |
The SIEM service utilizes threat intelligence to detect threats that can exploit potential vulnerabilities against your managed network.
Events are triggered when conditions on the monitored system meet or exceed predefined criteria (the “Criteria”). Since the Criteria are established and optimized over time, the first thirty (30) days after deployment of the SIEM services will be used to identify a baseline of the Client’s environment and user behavior. During this initial thirty (30) day period, Client may experience some “false positives” or, alternatively, during this period not all anomalous activities may be detected.
Note: The SIEM service is a monitoring and alert-based system only; remediation of detected or actual threats are not within the scope of this service and may require Client to retain WheelHouse IT’s services on a time and materials basis.
Primary endpoint security layer. Software agents installed in covered server devices protect against malware and prevents intruder access. Used in coordination with other endpoint security layers and security solutions to form a comprehensive defense strategy.
All software (including software installed on HaaS Equipment) and software as a service provided to you by or through WheelHouse IT is licensed, not sold, to you by a Third Party Provider (“Software”). In addition to any Software-related requirements described in the MSA, software may also be subject to end user license agreements (EULAs), acceptable use policies (AUPs), and other restrictions all of which must be strictly followed by you and any of your authorized users.
When installing/implementing software licenses in the managed environment or as part of the Services, we may accept (and you agree that we may accept) any required EULAs or AUPs on your behalf. You should assume that all Software has an applicable EULA and/or AUP to which your authorized users and you must adhere. If you have any questions or require a copy of the EULA or AUP, please contact us.
Updates and patching varies by the type of hardware, operating systems and installed software, but may include:
Important: There are additional terms related to the VoIP service, including your use of E911 features, toward the end of this Services Guide. Please read them carefully. You may be required to sign an additional consent form indicating your understanding and acceptance of the limitations of 911 dialing using the VoIP services.
We or our designated Third Party Provider will provide sufficient space and bandwidth to host your designated website (“Website”) which, except for Scheduled Downtime or force majeure events, will be available on a 24×7 basis. The Website will be hosted on a server that may be shared between many customers; however, the Website will be given a unique address (DNS).
Client, as well as any visitors to the Website, must comply with our Acceptable Use Policy which is located at the end of this Services Guide.
Please note: Any Wi-Fi devices, such as access points or routers, that are supplied by Client cannot be older than five (5) years from the applicable device’s original date of manufacture, and in all cases must be supported by the manufacturer of the device(s).
Primary endpoint security layer. Software agents installed in covered devices protect against malware and prevent intruder access. Used in coordination with other endpoint security layers and security solutions to create a comprehensive defensive strategy.
Software agents installed in covered workstations report status and IT-related events on a 24×7 basis; alerts are generated and responded to by Wheelhouse IT.
Managed Services will be applied to the devices on which we install software monitoring agents, network devices we are able to identify and access, or other devices as identified in a Quote (“Covered Hardware”). You may request a list of Covered Hardware once all software agents have been installed by contacting our support technicians.
The Services will apply to software that the applicable hardware manufacturer identifies as being necessary to support the Covered Hardware (i.e., operating systems) as well as software licensed through us (i.e., Office 365) (“Supported Software”); provided, however, that all Supported Software must, at all times, be properly licensed and under a maintenance and support agreement from the Supported Software’s manufacturer. We may, in our discretion, assist you in coordinating support for other software.
In this Services Guide, Covered Hardware and Supported Software will be referred to as the “Environment” or “Covered Equipment.” Coverage for non-Supported Software is outside of the scope of the Quote and, if provided to you, will be provided to you on a “best effort” basis only with no guarantee of remediation, and will be billed to you on a time and materials basis. Should our technicians provide you with general advice concerning non-Supported Software, the provision of that advice should be viewed as an accommodation to you, and not as a continuing obligation or guarantee by WheelHouse IT to continue to provide such support or advice to you.
If we are unable to remediate an issue with non-Supported Software, then you will be required to contact the manufacturer/distributor of the software for further support. Please note: Manufacturers/distributors of such software may charge fees, some of which may be significant, for technical support; therefore, we strongly recommend that you maintain service or support contracts for all non-Supported Software (“Service Contract”). If you request that we facilitate technical support for non-Supported Software, then if you have a Service Contract in place, our facilitation services will be provided at no additional cost to you.
From time to time, we may also provide the Services on a “per user” and/or “per device” basis, as detailed in the Quote. All devices must (i) be owned or leased by Client and used primarily for business, (ii) be regularly connected to Client’s managed network, and (iii) have installed on it, by WheelHouse IT, a software agent through which we (or our designated Third Party Providers) can monitor the device.
Services will be provided remotely unless, in our discretion, we determine that an onsite visit is required. WheelHouse IT visits will be scheduled in accordance with the priority assigned to the issue (below) and are subject to technician availability. Unless we agree otherwise, all onsite Services will be provided at Client’s primary business location. Additional fees may apply for onsite visits: Please review the Service Level section below for more details.
Term; Termination
The Services will commence, and billing will begin, on the date indicated in the Quote (“Commencement Date”) and will continue through the initial term listed in the Quote (“Initial Term”). We reserve the right to delay the Commencement Date until all onboarding services (if any) are completed, and all deficiencies / revisions identified in the initial audit / diagnostic services or onboarding services (if any) are addressed or remediated to WheelHouse IT’s satisfaction.
The Services will continue through the Initial Term until terminated as provided in the MSA, the Quote, or as indicated in this section (the “Service Term”).
Per Seat/Per Device Licensing: Regardless of the reason for the termination of the Services, you will be required to pay for all per seat or per device licenses that we acquire on your behalf. Please see “Access Licensing” in the Fees section below for more details.
Removal of Software Agents; Return of Firewall & Backup Appliances: Unless we expressly direct you to do so, you will not remove or disable, or attempt to remove or disable, any software agents that we installed in the managed environment or any of the devices on which we installed software agents. Doing so without our guidance may make it difficult or impracticable to remove the software agents, which could result in network vulnerabilities and/or the continuation of license fees for the software agents for which you will be responsible, and/or the requirement that we remediate the situation at our then-current hourly rates, for which you will also be responsible. Depending on the particular software agent and the costs of removal, we may elect to keep the software agent in the managed environment but in a dormant and/or unused state.
The scheduling, fees and provision of the Services are based upon the following assumptions and minimum requirements:
Exclusions. Services that are not expressly described in the Quote will be Out of Scope Services and will not be provided to Client unless otherwise agreed, in writing (email is sufficient for this purpose) by WheelHouse IT, or unless such services are reasonably required to respond to or mitigate against a critical or emergency situation. Without limiting the foregoing, the following services are expressly excluded, and if required to be performed, must be agreed upon by WheelHouse IT in writing:
Response, repair, and/or remediation services (as applicable) will be provided only during our business hours (currently M-F, 8 AM – 6 PM Eastern Time, excluding legal holidays and WheelHouse IT-observed holidays as listed below), unless otherwise specifically stated in the Quote or as otherwise described below.\
We will respond to problems, errors, or interruptions in the provision of the Services during business hours in the timeframe(s) described below. Severity levels will be determined by WheelHouse IT in our discretion after consulting with the Client. All remediation services will initially be attempted remotely; WheelHouse IT will provide onsite service only if remote remediation is ineffective and, under all circumstances, only if covered under the Service plan selected by Client.
Critical / Service Not Available
(e.g., all users and functions unavailable)
Response within two (2) business hours after notification.
Significant Degradation
(e.g., large number of users or business critical functions affected)
Response within four (4) business hours after notification.
Limited Degradation
(e.g., limited number of users or functions affected, business process can continue).
Response within eight (8) business hours after notification.
Small Service Degradation
(e.g., business process can continue, one user affected). Response within two (2) business days after notification.
Long Term Project, Preventative Maintenance Response within four (4) business days after notification.
* All time frames are calculated per issue and are calculated beginning with the time that a Service Ticket is initiated by Client for the applicable issue / problem through WheelHouse IT’s designated online support help desk, support email address, or by telephone at the WheelHouse IT’s support telephone number; provided, however, that for severity levels requiring a response time of four (4) business hours or less, Client must verbally confirm the receipt of the Service Ticket with WheelHouse IT (i.e., through the support telephone number). Each request for services must include information sufficient to identify the issue and determine its service priority level. Notifications received in any manner other than described herein may result in a delay in the provision of remediation efforts.
Support During Off-Hours/Non-Business Hours: Technical support provided outside of our normal business hours is offered on a case-by-case basis and is subject to technician availability. If WheelHouse IT agrees to provide off-hours/non-business hours support (“Non-Business Hour Support”), then WheelHouse IT reserves the right to provide that support on a time and materials basis as an Out of Scope Service for such service.
All hourly services are billed in 15 minute increments, and partial increments are rounded to the next highest increment. A one (1) hour minimum applies to all Non-Business Hour Support.
WheelHouse IT-Observed Holidays: WheelHouse IT observes the following holidays:
Service Credits: Our service level target is 90% as measured over a calendar month (“Target Service Level”). If we fail to adhere to the Target Service Level and Client timely brings that failure to our attention in writing (as per the requirements of the MSA), then Client will be entitled to receive a pro-rated service credit equal to 1/30 of that calendar month’s recurring service fees (excluding hard costs, licenses, etc.) for each day on which the Target Service Level is missed. Under no circumstances shall credits exceed 30% of the total monthly recurring service fees under an applicable Quote.
If WheelHouse IT receives any credits from a Third Party Provider for the failure of a Third Party Service provided to Client, WheelHouse IT shall pass on such credit, without deduction, to Client. WheelHouse IT shall have no obligation to seek such credits but shall cooperate with Client to do so upon Client’s request and subject to the service level and other terms of such Third Party Provider.
The fees for the Services will be as indicated in the Quote.
Reconciliation. Fees for certain Third Party Services that we facilitate or resell to you may begin to accrue prior to the “go-live” date of other applicable Services. (For example, Microsoft Azure or AWS-related fees begin to accrue on the first date on which we start creating and/or configuring certain hosted portions of the Environment; however, the Services that rely on Microsoft Azure or AWS may not be available to you until a future date). You understand and agree that you will be responsible for the payment of all fees for Third Party Services that are required to begin prior to the “go-live” date of Services, and we reserve the right to reconcile amounts owed for those fees by including those fees on your monthly invoices.
Changes to Environment. Initially, you will be charged the monthly fees indicated in the Quote. Thereafter, if the managed environment changes, or if the number of authorized users accessing the managed environment changes, then you agree that the fees will be automatically and immediately modified to accommodate those changes.
Travel Time. If onsite services are provided, we will travel up to 45 minutes from our office to your location at no charge. Time spent traveling beyond 45 minutes (e.g., locations that are beyond 45 minutes from our office, occasions on which traffic conditions extend our drive time beyond 45 minutes one-way, etc.) will be billed to you at our then current hourly rates. In addition, you will be billed for all tolls, parking fees, and related expenses that we incur if we provide onsite services to you.
Appointment Cancellations. You may cancel or reschedule any appointment with us at no charge by providing us with notice of cancellation at least one business day in advance. If we do not receive timely a notice of cancellation/re-scheduling, or if you are not present at the scheduled time or if we are otherwise denied access to your premises at a pre-scheduled appointment time, then you agree to pay us a cancellation fee equal to two (2) hours of our normal consulting time (or non-business hours consulting time, whichever is appropriate), calculated at our then-current hourly rates.
Access Licensing. One or more of the Services may require us to purchase certain “per seat” or “per device” licenses (often called “Access Licenses”) from one or more Third Party Providers. (Microsoft “New Commerce Experience” licenses as well as Cisco Meraki “per device” licenses are examples of Access Licenses.) Access Licenses cannot be canceled once they are purchased and often cannot be transferred to any other customer. For that reason, you understand and agree that regardless of the reason for termination of the Services, fees for Access Licenses are non-mitigatable and you are required to pay for all applicable Access Licenses in full for the entire term of those licenses. Provided that you have paid for the Access Licenses in full, you will be permitted to use those licenses until they expire.
Configuration of Third Party Services
Certain Third Party Services provided to you under an Order or as described in this Services Guide may provide you with administrative access through which you could modify the configurations, features, and/or functions (“Configurations”) of those services. However, any modifications of Configurations made by you without our authorization could disrupt the Services and/or cause a significant increase in the fees charged for those Third Party Services or result in out of scope fees for Services to remediate issues. For that reason, we strongly advise you to refrain from changing the Configurations unless we authorize those changes. You will be responsible for paying any increased fees or costs arising from or related to changes to the Configurations.
Modification of Environment
Changes made to the Environment without our prior authorization or knowledge may have a substantial, negative impact on the provision and effectiveness of the Services and may impact the fees charged under the Quote. You agree to refrain from moving, modifying, or otherwise altering any portion of the Environment without our consent. For example, you agree to refrain from adding or removing hardware from the Environment, installing applications on the Environment, or modifying the configuration or log files of the Environment without our prior knowledge or consent. Any modifications of the Environment made by you without our authorization could disrupt the Services, cause a significant increase in the fees charged for Third Party Services or result in out of scope fees for Services to remediate issues.
Anti-Malware
Our anti-malware solution will generally protect the Environment from becoming infected with new viruses and malware (“Malware”); however, Malware that exists in the Environment at the time that the security solution is implemented may not be capable of being removed without additional services, for which a charge may be incurred. We do not warrant or guarantee that all Malware will be capable of being detected, avoided, or removed, or that any data erased, corrupted, or encrypted by malware will be recoverable. To improve security awareness, you agree that WheelHouse IT or its designated Third Party Provider may transfer information about the results of processed files, information used for URL reputation determination, security risk tracking, and statistics for protection against spam and malware. Any information obtained in this manner does not and will not contain any personal or confidential information.
Breach/Cyber Security Incident Recovery
Unless otherwise expressly stated in the Quote, the scope of the Services does not include the remediation and/or recovery from a Security Incident (defined below). Such services, if requested by you, will be provided on a time and materials basis under our then-current hourly labor rates. Given the varied number of possible Security Incidents, we cannot and do not warrant or guarantee (i) Security Incidents will not occur; (ii) the amount of time required to remediate the effects of a Security Incident (or that recovery will be possible under all circumstances), or (iii) that all data or systems impacted by the incident will be recoverable or remediated. For the purposes of this paragraph, a Security Incident means any unauthorized or impermissible access to or use of the Environment, or any unauthorized or impermissible disclosure of Client’s confidential information (such as user names, passwords, etc.), that (i) compromises the security or privacy of the information or applications in, or the structure or integrity of, the managed environment, or (ii) prevents normal access to the managed environment, or impedes or disrupts the normal functions of the managed environment. You will notify us if you become aware of a Security Incident. Similarly, we will notify you when we become aware of a Security Incident. We Advise advise you to contact your insurance carrier when a Security Incident occurs and to engage (typically through your insurance carrier) a third party incident response service. Nevertheless, we may take actions prior to your engaging such third party in response to or related to the Security Incident (both before and after it is identified), whether deemed necessary and appropriate by us (in our sole discretion) or as directed by you. You understand and agree that with respect to any such actions taken by WheelHouse IT may adversely impact future forensic analysis.
Upon the conclusion of each investigation of each Security Incident, you agree promptly to share with WheelHouse IT the results of each investigation of each Security Incident, and upon your or WheelHouse IT’s request, conduct a “lessons learned” meeting to review the Security Incident’s root causes, response and/or changes to Services, policies or procedures.
Environmental Factors
Exposure to environmental factors, such as water, heat, cold, or varying lighting conditions, may cause installed equipment to malfunction. Unless expressly stated in the Quote, we do not warrant or guarantee that installed equipment will operate error-free or in an uninterrupted manner, or that any video or audio equipment will clearly capture and/or record the details of events occurring at or near such equipment under all circumstances.
Fair Usage Policy
Our Fair Usage Policy (“FUP”) applies to all Services that are described or designated as “unlimited” or which are not expressly capped in the number of available usage hours per month. An “unlimited” Service designation means that, subject to the terms of this FUP, you may use the applicable Service as reasonably necessary for you to enjoy the use and benefit of the Service without incurring additional time-based or usage-based costs. However, unless expressly stated otherwise in the Quote, all unlimited Services are provided during our normal business hours only and are subject to our technicians’ availabilities, which cannot always be guaranteed. In addition, we reserve the right to assign our technicians as we deem necessary to handle issues that are more urgent, critical, or pressing than the request(s) or issue(s) reported by you. Consistent with this FUP, you agree to refrain from (i) creating urgent support tickets for non-urgent or non-critical issues, (ii) requesting excessive support services that are inconsistent with normal usage patterns in the industry (e.g., requesting support in lieu of training), (iii) requesting support or services that are intended to interfere, or may likely interfere, with our ability to provide our Services to our other customers.
Hosted Email
You are solely responsible for the proper use of any hosted email service provided to you (“Hosted Email”).
Hosted Email solutions are subject to our and Third Party Providers’ acceptable use policies (“AUPs”), and your use of Hosted Email must comply with those AUPs.
Acceptable Use Policy
In all cases, you agree to refrain from uploading, posting, transmitting or distributing (or permitting any of your authorized users to upload, post, transmit or distribute) any prohibited content, which is generally content that (i) is obscene, illegal, or intended to advocate or induce the violation of any law, rule or regulation, or (ii) violates the intellectual property rights or privacy rights of any third party, or (iii) mischaracterizes you, and/or is intended to create a false identity or to otherwise attempt to mislead any person as to the identity or origin of any communication, or (iv) interferes or disrupts the Services, or (v) contains Viruses, trojan horses or any other malicious code or programs. In addition, you must not use the Hosted Email for the purpose of sending unsolicited commercial electronic messages (“SPAM”) in violation of any federal or state law. WheelHouse IT reserves the right, but not the obligation, to suspend Client’s access to the Hosted Email and/or all transactions occurring under Client’s Hosted Email account(s) if WheelHouse IT believes, in its discretion, that Client’s email account(s) is/are being used in an improper or illegal manner.
Backup (BDR) Services
All data transmitted over the Internet may be subject to malware and computer contaminants such as viruses, worms and trojan horses, as well as attempts by unauthorized users, such as hackers, to access or damage Client’s data. Neither WheelHouse IT nor its designated affiliates will be responsible for the outcome or results of such activities.
BDR services require a reliable, always-connected internet solution. Data backup and recovery time will depend on the speed and reliability of your internet connection. Internet and telecommunications outages will prevent the BDR services from operating correctly. In addition, all computer hardware is prone to failure due to equipment malfunction, telecommunication-related issues, etc., for which we will be held harmless. Due to technology limitations, all computer hardware, including communications equipment, network servers and related equipment, has an error transaction rate that can be minimized, but not eliminated. WheelHouse IT cannot and does not warrant that data corruption or loss will be avoided, and Client agrees that WheelHouse IT shall be held harmless if such data corruption or loss occurs. Client is strongly advised to keep a local backup of all of the stored data to mitigate against the unintentional loss of data.
Procurement
Equipment and software procured by WheelHouse IT on Client’s behalf (“Procured Equipment”) may be covered by one or more manufacturer warranties, which will be passed through to Client to the greatest extent possible. By procuring equipment or software for Client, WheelHouse IT does not make any warranties or representations regarding the quality, integrity, or usefulness of the Procured Equipment. Certain equipment or software, once purchased, may not be returnable or, in certain cases, may be subject to third party return policies and/or re-stocking fees, all of which shall be Client’s responsibility in the event that a return of the Procured Equipment is requested. WheelHouse IT is not a warranty service or repair center. WheelHouse IT will facilitate the return or warranty repair of Procured Equipment; however, Client understands and agrees that (i) the return or warranty repair of Procured Equipment is governed by the terms of the warranties (if any) governing the applicable Procured Equipment, for which WheelHouse IT will be held harmless, and (ii) WheelHouse ITIT is not responsible for the quantity, condition, or timely delivery of the Procured Equipment once the equipment has been tendered to the designated shipping or delivery courier.
Business Review / IT Strategic Planning Meetings
We strongly suggest that you participate in business review/strategic planning meetings as may be requested by us from time to time. These meetings are intended to educate you about recommended (and potentially crucial) modifications to your IT environment, as well as to discuss your company’s present and future IT-related needs. These reviews can provide you with important insights and strategies to make your managed IT environment more efficient and secure. You understand that by suggesting a particular service or solution, we are not endorsing any specific manufacturer or service provider.
VCTO or VCIO Services
Unless specified in an Order, the Services do not include advice and suggestions to you in a capacity typically provided by a virtual chief technology or information officer, and so any such advice or suggestions will be for your informational and/or educational purposes only. WheelHouse IT will not hold an actual director or officer position in Client’s company, and we will neither hold nor maintain any fiduciary relationship with, or decision making authority for, Client. Under no circumstances shall Client list or place WheelHouse IT on Client’s corporate records or accounts.
Sample Policies, Procedures.
From time to time, we may provide you with sample (i.e., template) policies and procedures for use in connection with Client’s business (“Sample Policies”). The Sample Policies are for your informational use only, and do not constitute or comprise legal or professional advice, and the policies are not intended to be a substitute for the advice of competent counsel. You should seek the advice of competent legal counsel prior to using or distributing the Sample Policies, in part or in whole, in any transaction. We do not warrant or guarantee that the Sample Policies are complete, accurate, or suitable for your (or your customers’) specific needs, or that you will reduce or avoid liability by utilizing the Sample Policies in your (or your customers’) business operations.
You understand and agree that security devices, alarms, or other security measures, both physical and virtual, may be tripped or activated during the penetration testing process, despite our efforts to avoid such occurrences. You will be solely responsible for notifying any monitoring company and all law enforcement authorities of the potential for “false alarms” due to the provision of the penetration testing services, and you agree to take all steps necessary to ensure that false alarms are not reported or treated as “real alarms” or credible threats against any person, place or property. Some alarms and advanced security measures, when activated, may cause the partial or complete shutdown of the Environment, causing substantial downtime and/or delay to your business activities. We will not be responsible for any claims, costs, fees or expenses arising or resulting from (i) any response to the penetration testing services by any monitoring company or law enforcement authorities, or (ii) the partial or complete shutdown of the Environment by any alarm or security monitoring device.
No Third Party Scanning
Unless we authorize such activity in writing, you will not conduct any test, nor request or allow any third party to conduct any test (diagnostic or otherwise), of the security system, protocols, processes, or solutions that we implement in the managed environment (“Testing Activity”). Any services required to diagnose or remediate errors, issues, or problems arising from unauthorized Testing Activity are not covered under the Quote, and if you request us (and we elect) to perform those services, those services will be billed to you at our then-current hourly rates.
Obsolescence
If at any time any portion of the managed environment becomes outdated, obsolete, reaches the end of its useful life, or acquires “end of support” status from the applicable device’s or software’s manufacturer (“Obsolete Element”), then we may designate the device or software as “unsupported” or “non-standard” and require you to update the Obsolete Element within a reasonable time period as stated in a written notice to you. If you do not replace the Obsolete Element reasonably promptly, then in our discretion we may (i) continue to provide the Services to the Obsolete Element using our “best efforts” only with no warranty or requirement of remediation whatsoever regarding the operability or functionality of the Obsolete Element, or (ii) eliminate the Obsolete Element from the scope of the Services by providing written notice to you (email is sufficient for this purpose). In any event, we make no representation or warranty whatsoever regarding any Obsolete Element or the deployment, service level guarantees, or remediation activities for any Obsolete Element. Any issues caused by the obsolescence of an Obsolete Element are out of scope.
You agree that you are responsible for the actions and behaviors of your users of the Services. In addition, you agree that neither Client, nor any of your employees or designated representatives, will use the Services in a manner that violates the laws, regulations, ordinances, or other such requirements of any jurisdiction.
In addition, Client agrees that neither it, nor any of its employees or designated representatives, will: transmit any unsolicited commercial or bulk email, will not engage in any activity known or considered to be “spamming” and carry out any “denial of service” attacks on any other website or Internet service; infringe on any copyright, trademark, patent, trade secret, or other proprietary rights of any third party; collect, attempt to collect, publicize, or otherwise disclose personally identifiable information of any person or entity without their express consent (which may be through the person or entity’s registration and/or subscription to Client’s services, in which case Client must provide a privacy policy which discloses any and all uses of information that you collect) or as otherwise required by law; or, undertake any action which is harmful or potentially harmful to WheelHouse IT or its infrastructure.
Client is solely responsible for ensuring that its login information is utilized only by Client and Client’s authorized users and agents. Client’s responsibility includes ensuring the secrecy and strength of user identifications and passwords. WheelHouse IT shall have no liability resulting from the unauthorized use of Client’s login information. If login information is lost, stolen, or used by unauthorized parties or if Client believes that any hosted applications or hosted data has been accessed by unauthorized parties, it is Client’s responsibility to notify WheelHouse IT immediately to request the login information be reset or unauthorized access otherwise be prevented. WheelHouse IT will use commercially reasonable efforts to implement such requests as soon as practicable after receipt of notice.
Licenses
If we are required to re-install or replicate any software provided by you as part of the Services, then it is your responsibility to verify that all such software is properly licensed. We reserve the right, but not the obligation, to require proof of licensing before installing, re-installing, or replicating software into the managed environment. The cost of acquiring licenses is not included in the scope of the Quote unless otherwise expressly stated therein.
The following terms and conditions apply to your use of any VoIP service that we facilitate for you or that is provided to you by a Third Party Provider of such service. Please note, by using VoIP services you agree to the provisions of the waiver at the end of this section. If you do not understand or do not agree with any of the terms below, you must not subscribe to, use, or rely upon any VoIP service and, instead, you must contact us immediately.
There is an important difference in how 9-1-1 (i.e., emergency) services can be dialed using a VoIP service as compared to a traditional telephone line. Calling emergency services using a VoIP service is referred to as “E911.”
Registration: You are responsible for activating the E911 dialing feature by registering the address where you will use the VoIP service. This will not be done for you, and you must take this step on your own initiative. To do this, you must log into your VoIP control panel and provide a valid physical address. If you do not take this step, then E911 services may not work correctly, or at all, using the VoIP service. Emergency service dispatchers will only send emergency personnel to a properly registered E911 service address.
Location: The address you provide in the control panel is the location to which emergency services (such as the fire department, the police department, etc.) will respond. For this reason, it is important that you correctly enter the location at which you are using the VoIP services. PO boxes are not proper addresses for registration and must not be used as your registered address. Please note, even if your account is properly registered with a correct physical address, (i) there may be a problem automatically transmitting a caller’s physical location to the emergency responders, even if the caller can reach the 911 call center, and (ii) a VoIP 911 call may go to an unstaffed call center administrative line or be routed to a call center in the wrong location. These issues are inherent to all VoIP systems and services. We will not be responsible for, and you agree to hold us harmless from, any issues, problems, incidents, damages (both bodily- and property-related), costs, expenses, and fees arising from or related to your failure to register timely and correctly your physical location information into the control panel.
Address Change(s): If you change the address used for E911 calling, the E911 services may not be available and/or may operate differently than expected. Moreover, if you do not properly and promptly register a change of address, then emergency services may be directed to the location where your services are registered and not where the emergency may be occurring. For that reason, you must register a change of address with us through the VoIP control panel no less than three (3) business days prior to your anticipated move/address change. Address changes that are provided to us with less than three (3) business days’ notice may cause incorrect/outdated information to be conveyed to emergency service personnel. If you are unable to provide us with at least three (3) business days’ notice of an address change, then you should not rely on the E911 service to provide correct physical location information to emergency service personnel. Under those circumstances, you must provide your correct physical location to emergency service dispatchers if you call them using the VoIP services.
If you do not register the VoIP service at your location and you dial 9-1-1, that call will be categorized as a “rogue 911 call.” If you are responsible for dialing a rogue 911 call, you will be charged a non-refundable and non-disputable fee of $250/call.
Power Loss: If you lose power or there is a disruption to power at the location where the VoIP services are used, then the E911 calling service will not function until power is restored. You should also be aware that after a power failure or disruption, you may need to reset or reconfigure the device prior to utilizing the service, including E911 dialing.
Internet Disruption: If your internet connection or broadband service is lost, suspended, terminated or disrupted, E911 calling will not function until the internet connection and/or broadband service is restored.
Account Suspension: If your account is suspended or terminated, then all E911 dialing services will not function.
Network Congestion: There may be a greater possibility of network congestion and/or reduced speed in the routing of E911 calls as compared to 911 dialing over traditional public telephone networks.
WAIVER: You hereby agree to release, indemnify, defend, and hold us and our officers, directors, representatives, agents, and any Third Party Provider that furnishes VoIP-related services to you, harmless from any and all claims, damages, losses, suits or actions, fines, penalties, costs and expenses (including, but not limited to, attorneys’ fees), whether suffered, made, instituted or asserted by you or by any other party or person (collectively, “Claims”) arising from or related to the VoIP services, including but not limited to any failure or outage of the VoIP services, incorrect routing or use of, or any inability to use, E911 dialing features. The foregoing waiver and release shall not apply to Claims arising from our gross negligence, recklessness, or willful misconduct.
If you need to contact our sales team for any reason please call by phone or email.
(877) 771-2384 option 2
Watch the video below and find out why you should fill out this form and start a conversation today.
"*" indicates required fields